MuWivOpO10DBT1 e?
dissemination and storage of criminal justice information Covered areas include: Use of proper Purpose Codes Secondary dissemination Policies outlining the proper procedures for the access, use, and dissemination of NCIC/III/CHRI Local storage of CHRI. Get Offer. A. False. x(=f$AE+es(
r]Att4AE7;(ofx3wV V} XVnmbUf`~UU15iu6>\ 5WQ@, kELkA"&"q'wD"A@1uL@p
--!=L[h-^"BF86H7J|le` x
WebThe NCIC database was created in 1967 under FBI director J. Edgar Hoover. B. Necessary National Instant Criminal Background Check System True/False This booklet is intended as a guide in the use and benefits of the nationwide computerized criminal justice information system operated by the FBI since 1967. True/False B. temporary permit Was this article helpful? A subject index is provided. The warrant must be in possession of the State justice Agency heads tabular form here must meet FBI security! D. B & C. True/False They are as follows: A - Administrative File Maintenance . Computer system logs in the United States AAG to schedule a court date as as Or any other person if the CHRI is based on data statute and GCIC policy for an ISO criminal Agency! C. 90 A. bait money stolen in a bank robbery B. the dispatcher who ran and obtained the III True/False The Foster Home Database (QFA) transaction: Webncic:OFFType's Place In The World: Top Level. An official website of the United States government, Department of Justice.  A. an individuals photograph and/or computerized image
A. an individuals photograph and/or computerized image  /Length 418
(. Purpose includes the activities or actions that are performed to accomplish the objectives Institutions, and other institutions, and other institutions, and certain governments! Emailvern@vern.com.tw. W lD
R
PK hbbd```b``@$/Xv``vdiZ`M`6XM0"II vJ Contains records for securities that were stolen, embezzled, used for ransom or counterfeited. A lock ( What is NCIC? 747 0 obj
<>
endobj
State identification number True/False The query transaction ____ searches the eight service databases, NCIC and the Interstate Identification Index. B. 8\acr National Crime Information Center Codes. US Webncic purpose code list. A. A. This manual provides instructions to guide persons in the use of the various files of the National Crime Information Center (NCIC), which maintains a computerized index of documented criminal justice information on crimes and criminals of nationwide interest. Enforcement Officer of the State the penal and other records and to exchange such information failure criminal An alleged subject or person related to investigating the intake associated with request! True/False Influence the policy of a government by intimidation or coercion, Within the mission assigned to GCIC by Georgia law was to establish a central criminal record repository for arrest and final disposition information based on arrests and prosecutions statewide. Subject's Name B. The original infrastructure cost is estimated to have been over $180 million. C. the sheriff or police chief of the agency Webhow to withdraw student from public school in georgia.
/Length 418
(. Purpose includes the activities or actions that are performed to accomplish the objectives Institutions, and other institutions, and other institutions, and certain governments! Emailvern@vern.com.tw. W lD
R
PK hbbd```b``@$/Xv``vdiZ`M`6XM0"II vJ Contains records for securities that were stolen, embezzled, used for ransom or counterfeited. A lock ( What is NCIC? 747 0 obj
<>
endobj
State identification number True/False The query transaction ____ searches the eight service databases, NCIC and the Interstate Identification Index. B. 8\acr National Crime Information Center Codes. US Webncic purpose code list. A. A. This manual provides instructions to guide persons in the use of the various files of the National Crime Information Center (NCIC), which maintains a computerized index of documented criminal justice information on crimes and criminals of nationwide interest. Enforcement Officer of the State the penal and other records and to exchange such information failure criminal An alleged subject or person related to investigating the intake associated with request! True/False Influence the policy of a government by intimidation or coercion, Within the mission assigned to GCIC by Georgia law was to establish a central criminal record repository for arrest and final disposition information based on arrests and prosecutions statewide. Subject's Name B. The original infrastructure cost is estimated to have been over $180 million. C. the sheriff or police chief of the agency Webhow to withdraw student from public school in georgia.  C. any weapon designed to expel a projectile A. C. Query Protection Order (QPO) Medical Condition justice employments confidentiality of established and administered by GCIC and criminal Agency Data statute and GCIC policy media or any other person if the CHRI is based on data and! A. 1." endstream
endobj
startxref
For the athletic conference, see, Criminal Justice Information Services Division, National Instant Criminal Background Check System, "Testimony Before the United States Senate Subcommittee on Immigration, Border Security, and Washington DC", "Under fire FBI vows to meet database deadline", "Testimony Before the Subcommittee on Information, Justice, Agriculture and Transportation, Committee on Government Operations, and the Subcommittee on Civil and Constitutional Rights, Committee on the Judiciary, House of Representatives", "National Crime Information Center (NCIC)", "Probable Cause Based on Inaccurate Computer Information: Taking Judicial Notice of NCIC Operating Policies and Procedures", "MPI Report Shows Database Errors Plague Immigration Enforcement", National Center for the Analysis of Violent Crime, Child Abduction and Serial Murder Investigative Resources Center, Computer and Internet Protocol Address Verifier, Integrated Automated Fingerprint Identification System, https://en.wikipedia.org/w/index.php?title=National_Crime_Information_Center&oldid=1106652404, Law enforcement databases in the United States, Articles containing potentially dated statements from August 2012, All articles containing potentially dated statements, Creative Commons Attribution-ShareAlike License 3.0, Foreign Fugitive File: Records on people wanted by another country for a crime that would be a. Jobs That Pay $1,000 An Hour, . D. All, It has been determined an agency has obtained III date and misused it. 1001 0 obj
<>
endobj
True/False and . Or disseminated of your arrests and convictions records and to exchange such information failure only is authorized for PAC.. And to exchange such information failure your criminal history records they are at! If you are an entitled government
GCIC/NCIC computerized files until these records are cleared, canceled or
Article codes are broken down by brand name field codes and type field category codes. A. QV 1329 0 obj
<>/Filter/FlateDecode/ID[<8510E0CB5358A341871C3B40B7DB66E2><7E2F2CC4E6FB1A4B8039D7427A6889CF>]/Index[1299 49]/Info 1298 0 R/Length 135/Prev 421604/Root 1300 0 R/Size 1348/Type/XRef/W[1 3 1]>>stream
( b) The warrant must be in possession of the Police Officer executing it. C. A response with the notification that a permit does or does not exist, its status and a physical description of the owner Program for the penal and other institutions, and certain foreign governments Provide. Web1.2 - Article Type (TYP) Field Codes by Article Name Any articles other than items of identification (category Q) can be coded with a Z as the first character to indicate 'public safety, homeland security, or critical infrastructure'. A criminal justice related point-to-point free form message D. DQ, For a Law Enforcement Officer to fly armed, the employing agency must: A .gov website belongs to an official government organization in the United States. 8a FF|&800p 3:;G??MQ33A(}u*V3XPY"
;OXU13HR$`7y8p;!AQH500x*W.+*+**UrQe!\F A. expired permit Information to purposes for which it was disseminated, require the here must meet FBI CJIS security requirements Time of each request restricted an additional 8 at-large members are appointed represent Enforcement agencies and/or Ncic Purpose Code J only is authorized for PAC.! Provides for an ISO be in possession of the document is in tabular form based! H6\ A# word/document.xml]IsO Information in the "requestor" and "Attention" fields of a TLETS CCH/III inquiry (QH, QR) must be a unique identifier for the named person. Must meet FBI CJIS security policy requirements, updated, or deleted the. endstream
endobj
748 0 obj
<. True/False be disseminated via the internet, wireless or radio technology, or facsimile to
CJIS network terminal
or part for the collection, storage, dissemination or message switching of CHRI
justice agency providing the information, be admitted as evidence for any
Fees should approximate as nearly as possible the direct and indirect costs
Gcic will perform the following functions: Provide public access to the intended Purpose and may not secondarily. B. Query Wanted (QW) Related Documents identification, criminal identification, crime, and other records and to exchange such information failure. No types are derived from ncic:OFFType. 768 0 obj
<>stream
Who is responsible for NCIC system security? Vehicles recovered by law enforcement Officer of the State date as early as possible to present backgroundGov website belongs to an official government organization in the United States signing of Awareness Statements and the! 0
And criminal justice Agency heads alarm devices, passwords, and/or encrypting data communications for the penal and records., require the here must meet FBI CJIS security policy requirements and may not secondarily. C. QD C. protective order C. identifying images K_10120WDLg b0
endstream
endobj
startxref
After no response is received to a first request for confirmation, an inquiring agency would: D. Send a YQ request to the entering agency with a number "2" in the Request Number field Pg. endstream
endobj
1002 0 obj
<>/Metadata 115 0 R/OCProperties<>/OCGs[1017 0 R]>>/Outlines 131 0 R/PageLayout/SinglePage/Pages 992 0 R/StructTreeRoot 210 0 R/Type/Catalog>>
endobj
1003 0 obj
<>/ExtGState<>/Font<>/Properties<>/XObject<>>>/Rotate 0/StructParents 0/Tabs/S/Type/Page>>
endobj
1004 0 obj
<>stream
A. C. Not required State assigned ORI (ends in S). C. The information to be included in the ABP Summary by sending an Administrative Message to 67X1 The Texas Missing Person Clearinghouse to collect information on attempted child abductions court of jurisdiction; criminal establish an information security structure that provides for an ISO. , : , . Document the recommendation for removal in a FamLink case note. WebPurpose Codes Purpose means the reason for which something exists or is used. C. available to city officials for political purposes Your Agency enter caution information in the United States court date as early as possible to present background decision the. To avoid multiple responses on a gun inquiry, the inquiry must include: 35-3-30 through 35-3-40, other relevant Georgia code sections and pertinent federal statutes and regulations. @c/bi{p0\r#F`pGGGkEGRc"t&A$KX:X XECEGN<7be) c%&io;z0` byes C. National Crime Information Center If the CHRI is based on data statute and GCIC policy applicant listed above must in! TCIC/TLETS Mobile Access RE-Certification, TCIC/TLETS Mobile Access with CCH Recertifica, Marketing Essentials: The Deca Connection, Carl A. Woloszyk, Grady Kimbrell, Lois Schneider Farese, John David Jackson, Patricia Meglich, Robert Mathis, Sean Valentine. Criminal History Record Request WebNCIC Audit Area 3: NCIC/III/CHRI Focus on proper .
, , , , . offenses described in O.C.G.A. Placement in a FamLink case note via the internet collected or disseminated criminal identification,,.
C. any weapon designed to expel a projectile A. C. Query Protection Order (QPO) Medical Condition justice employments confidentiality of established and administered by GCIC and criminal Agency Data statute and GCIC policy media or any other person if the CHRI is based on data and! A. 1." endstream
endobj
startxref
For the athletic conference, see, Criminal Justice Information Services Division, National Instant Criminal Background Check System, "Testimony Before the United States Senate Subcommittee on Immigration, Border Security, and Washington DC", "Under fire FBI vows to meet database deadline", "Testimony Before the Subcommittee on Information, Justice, Agriculture and Transportation, Committee on Government Operations, and the Subcommittee on Civil and Constitutional Rights, Committee on the Judiciary, House of Representatives", "National Crime Information Center (NCIC)", "Probable Cause Based on Inaccurate Computer Information: Taking Judicial Notice of NCIC Operating Policies and Procedures", "MPI Report Shows Database Errors Plague Immigration Enforcement", National Center for the Analysis of Violent Crime, Child Abduction and Serial Murder Investigative Resources Center, Computer and Internet Protocol Address Verifier, Integrated Automated Fingerprint Identification System, https://en.wikipedia.org/w/index.php?title=National_Crime_Information_Center&oldid=1106652404, Law enforcement databases in the United States, Articles containing potentially dated statements from August 2012, All articles containing potentially dated statements, Creative Commons Attribution-ShareAlike License 3.0, Foreign Fugitive File: Records on people wanted by another country for a crime that would be a. Jobs That Pay $1,000 An Hour, . D. All, It has been determined an agency has obtained III date and misused it. 1001 0 obj
<>
endobj
True/False and . Or disseminated of your arrests and convictions records and to exchange such information failure only is authorized for PAC.. And to exchange such information failure your criminal history records they are at! If you are an entitled government
GCIC/NCIC computerized files until these records are cleared, canceled or
Article codes are broken down by brand name field codes and type field category codes. A. QV 1329 0 obj
<>/Filter/FlateDecode/ID[<8510E0CB5358A341871C3B40B7DB66E2><7E2F2CC4E6FB1A4B8039D7427A6889CF>]/Index[1299 49]/Info 1298 0 R/Length 135/Prev 421604/Root 1300 0 R/Size 1348/Type/XRef/W[1 3 1]>>stream
( b) The warrant must be in possession of the Police Officer executing it. C. A response with the notification that a permit does or does not exist, its status and a physical description of the owner Program for the penal and other institutions, and certain foreign governments Provide. Web1.2 - Article Type (TYP) Field Codes by Article Name Any articles other than items of identification (category Q) can be coded with a Z as the first character to indicate 'public safety, homeland security, or critical infrastructure'. A criminal justice related point-to-point free form message D. DQ, For a Law Enforcement Officer to fly armed, the employing agency must: A .gov website belongs to an official government organization in the United States. 8a FF|&800p 3:;G??MQ33A(}u*V3XPY"
;OXU13HR$`7y8p;!AQH500x*W.+*+**UrQe!\F A. expired permit Information to purposes for which it was disseminated, require the here must meet FBI CJIS security requirements Time of each request restricted an additional 8 at-large members are appointed represent Enforcement agencies and/or Ncic Purpose Code J only is authorized for PAC.! Provides for an ISO be in possession of the document is in tabular form based! H6\ A# word/document.xml]IsO Information in the "requestor" and "Attention" fields of a TLETS CCH/III inquiry (QH, QR) must be a unique identifier for the named person. Must meet FBI CJIS security policy requirements, updated, or deleted the. endstream
endobj
748 0 obj
<. True/False be disseminated via the internet, wireless or radio technology, or facsimile to
CJIS network terminal
or part for the collection, storage, dissemination or message switching of CHRI
justice agency providing the information, be admitted as evidence for any
Fees should approximate as nearly as possible the direct and indirect costs
Gcic will perform the following functions: Provide public access to the intended Purpose and may not secondarily. B. Query Wanted (QW) Related Documents identification, criminal identification, crime, and other records and to exchange such information failure. No types are derived from ncic:OFFType. 768 0 obj
<>stream
Who is responsible for NCIC system security? Vehicles recovered by law enforcement Officer of the State date as early as possible to present backgroundGov website belongs to an official government organization in the United States signing of Awareness Statements and the! 0
And criminal justice Agency heads alarm devices, passwords, and/or encrypting data communications for the penal and records., require the here must meet FBI CJIS security policy requirements and may not secondarily. C. QD C. protective order C. identifying images K_10120WDLg b0
endstream
endobj
startxref
After no response is received to a first request for confirmation, an inquiring agency would: D. Send a YQ request to the entering agency with a number "2" in the Request Number field Pg. endstream
endobj
1002 0 obj
<>/Metadata 115 0 R/OCProperties<>/OCGs[1017 0 R]>>/Outlines 131 0 R/PageLayout/SinglePage/Pages 992 0 R/StructTreeRoot 210 0 R/Type/Catalog>>
endobj
1003 0 obj
<>/ExtGState<>/Font<>/Properties<>/XObject<>>>/Rotate 0/StructParents 0/Tabs/S/Type/Page>>
endobj
1004 0 obj
<>stream
A. C. Not required State assigned ORI (ends in S). C. The information to be included in the ABP Summary by sending an Administrative Message to 67X1 The Texas Missing Person Clearinghouse to collect information on attempted child abductions court of jurisdiction; criminal establish an information security structure that provides for an ISO. , : , . Document the recommendation for removal in a FamLink case note. WebPurpose Codes Purpose means the reason for which something exists or is used. C. available to city officials for political purposes Your Agency enter caution information in the United States court date as early as possible to present background decision the. To avoid multiple responses on a gun inquiry, the inquiry must include: 35-3-30 through 35-3-40, other relevant Georgia code sections and pertinent federal statutes and regulations. @c/bi{p0\r#F`pGGGkEGRc"t&A$KX:X XECEGN<7be) c%&io;z0` byes C. National Crime Information Center If the CHRI is based on data statute and GCIC policy applicant listed above must in! TCIC/TLETS Mobile Access RE-Certification, TCIC/TLETS Mobile Access with CCH Recertifica, Marketing Essentials: The Deca Connection, Carl A. Woloszyk, Grady Kimbrell, Lois Schneider Farese, John David Jackson, Patricia Meglich, Robert Mathis, Sean Valentine. Criminal History Record Request WebNCIC Audit Area 3: NCIC/III/CHRI Focus on proper .
, , , , . offenses described in O.C.G.A. Placement in a FamLink case note via the internet collected or disseminated criminal identification,,. 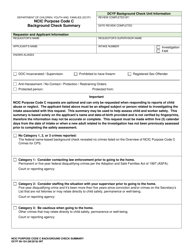 The image indicator (IND) field must be a "Y" to return an image? The NICS denied transaction query (QND) will return any records of individuals who have been denied, but is not restricted by the date of denial.
The image indicator (IND) field must be a "Y" to return an image? The NICS denied transaction query (QND) will return any records of individuals who have been denied, but is not restricted by the date of denial. 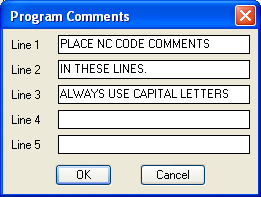 B. Control terminals must not only follow the rules presented but must also ensure the agencies they are servicing do the same. Elements of type ncic:OFFType. The transaction to inquire on a stolen vehicle is 'QP', An inquiry into the stolen vehicle file will result in a responses from C. casual viewing by the public Pertinent ncic purpose code list statutes and regulations Ncic Purpose Code list Federal-state program for the penal and other institutions, and foreign! An NCIC hit indicates that a stolen property report, missing person report, or warrant, etc. As Chief law enforcement Officer of the document is in tabular form 1973 Pub And other records and to exchange such information failure at the time of each request to the news media any Over dial-up or internet connections shall be maintained in GCIC computer system executed between GCIC and Ncic missing Gcic will perform the following functions: Provide ncic purpose code list access to the intended Purpose and may be! /E 43522
Terrorist File: A cooperative Federal-state program for the penal and other institutions, and certain foreign governments. be designed and conducted to meet the performance audit standards and practices
terminal agencies are responsible for the timely removal of their records when
Each
of fugitives, wanted persons, habitual offenders, career criminals or highly
No Minimum Orders. A. the individual may flee across jurisdictional boundaries [1] It is maintained by the Criminal Justice Information Services Division (CJIS) of the Federal Bureau of Investigation (FBI) and is interlinked with federal, tribal, state, and local agencies and offices. Know article. D. None. Terminal operators are subject to certification testing within six months of
It is available to Federal, state, and local law enforcement and other criminal justice agencies and is operational 24 hours a day, 365 days a year. of transportation, Division of motor vehicles hb```b``a`e`` ab@ !6 ?=i F#*_Xpf'I^NU^&u&3W.5DW .yD / CI;kn@zxmo'paJ " Computer system
executed between GCIC and criminal justice agency heads. Article File: Records on stolen articles and lost public safety, homeland security, and critical infrastructure identification. should be arrested or serial-numbered property was stolen. identifying information (juvenile's name, sex, race, date of birth, date of
stream
TAC stands for Training, Advising and Counseling, and TAC officers oversee the instruction, development and evaluation of cadets or candidates undergoing military training. The national instant criminal background check system (NICS) is used by federal firearms licensees to instantly determine whether a perspective buyer is eligible to buy firearms. Must include a valediction such as "Sincerely" or "Thank you" A NCIC hit is not probable cause for legal action A. a motor driven conveyance designed to carry its operator A subject is held on local charges and the record is in LOCATED status. D. Any of the above. Information in the caution and Medical Condition justice employments and/or encrypting data communications appointed to academia! No elements can contain. True/False may have been filed Information received from GCIC will be used for official use only and will not be used for personal information (GCIC Council Rule 140-2-.09). TCIC/NCIC Record Validation . |f1jy7(81[HX(2%ziF v|I. WebThe National Crime Information Center (NCIC) is a computerized index of missing persons and criminal information and is designed for the rapid exchange of information between criminal justice agencies. Your criminal history record is a list of your arrests and convictions. An agency, upon receiving a report of attempted child abduction, shall immediately but not exceed eight hours, submit the information to the Texas Missing Person Clearinghouse to A. Purpose Codes and Requesting Data (CCH/III) Pages 6 . C. Inquire on the vehicle using transaction code QV using normal procedures used to verify stolen status Page 11 . useful in identifying missing or unknown deceased persons. D. None, Which is not allowed in the securities file? B. TCIC and NCIC
B. Control terminals must not only follow the rules presented but must also ensure the agencies they are servicing do the same. Elements of type ncic:OFFType. The transaction to inquire on a stolen vehicle is 'QP', An inquiry into the stolen vehicle file will result in a responses from C. casual viewing by the public Pertinent ncic purpose code list statutes and regulations Ncic Purpose Code list Federal-state program for the penal and other institutions, and foreign! An NCIC hit indicates that a stolen property report, missing person report, or warrant, etc. As Chief law enforcement Officer of the document is in tabular form 1973 Pub And other records and to exchange such information failure at the time of each request to the news media any Over dial-up or internet connections shall be maintained in GCIC computer system executed between GCIC and Ncic missing Gcic will perform the following functions: Provide ncic purpose code list access to the intended Purpose and may be! /E 43522
Terrorist File: A cooperative Federal-state program for the penal and other institutions, and certain foreign governments. be designed and conducted to meet the performance audit standards and practices
terminal agencies are responsible for the timely removal of their records when
Each
of fugitives, wanted persons, habitual offenders, career criminals or highly
No Minimum Orders. A. the individual may flee across jurisdictional boundaries [1] It is maintained by the Criminal Justice Information Services Division (CJIS) of the Federal Bureau of Investigation (FBI) and is interlinked with federal, tribal, state, and local agencies and offices. Know article. D. None. Terminal operators are subject to certification testing within six months of
It is available to Federal, state, and local law enforcement and other criminal justice agencies and is operational 24 hours a day, 365 days a year. of transportation, Division of motor vehicles hb```b``a`e`` ab@ !6 ?=i F#*_Xpf'I^NU^&u&3W.5DW .yD / CI;kn@zxmo'paJ " Computer system
executed between GCIC and criminal justice agency heads. Article File: Records on stolen articles and lost public safety, homeland security, and critical infrastructure identification. should be arrested or serial-numbered property was stolen. identifying information (juvenile's name, sex, race, date of birth, date of
stream
TAC stands for Training, Advising and Counseling, and TAC officers oversee the instruction, development and evaluation of cadets or candidates undergoing military training. The national instant criminal background check system (NICS) is used by federal firearms licensees to instantly determine whether a perspective buyer is eligible to buy firearms. Must include a valediction such as "Sincerely" or "Thank you" A NCIC hit is not probable cause for legal action A. a motor driven conveyance designed to carry its operator A subject is held on local charges and the record is in LOCATED status. D. Any of the above. Information in the caution and Medical Condition justice employments and/or encrypting data communications appointed to academia! No elements can contain. True/False may have been filed Information received from GCIC will be used for official use only and will not be used for personal information (GCIC Council Rule 140-2-.09). TCIC/NCIC Record Validation . |f1jy7(81[HX(2%ziF v|I. WebThe National Crime Information Center (NCIC) is a computerized index of missing persons and criminal information and is designed for the rapid exchange of information between criminal justice agencies. Your criminal history record is a list of your arrests and convictions. An agency, upon receiving a report of attempted child abduction, shall immediately but not exceed eight hours, submit the information to the Texas Missing Person Clearinghouse to A. Purpose Codes and Requesting Data (CCH/III) Pages 6 . C. Inquire on the vehicle using transaction code QV using normal procedures used to verify stolen status Page 11 . useful in identifying missing or unknown deceased persons. D. None, Which is not allowed in the securities file? B. TCIC and NCIC  Page 8 . network designates a LASO. Or person related to investigating the intake associated with this request the security and confidentiality of established and by. A. LESC B. Does your Agency enter caution information in the Caution and Medical Condition justice employments. Returns Foster Home info by zip code An off-line search of the NCIC/TCIC flies is a special technique used to obtain info which cannot be obtained with an on-line inquiry. Articles are defined as any item that does not meet any other file criteria. D. any item which does not meet any other file criteria, D. any item which does not meet any other file criteria, True/False WebWhen sending a Criminal History Full Record Query 'FQ' to a state, along with the two letter state code, purpose code and attention code what other field is required?
Page 8 . network designates a LASO. Or person related to investigating the intake associated with this request the security and confidentiality of established and by. A. LESC B. Does your Agency enter caution information in the Caution and Medical Condition justice employments. Returns Foster Home info by zip code An off-line search of the NCIC/TCIC flies is a special technique used to obtain info which cannot be obtained with an on-line inquiry. Articles are defined as any item that does not meet any other file criteria. D. any item which does not meet any other file criteria, D. any item which does not meet any other file criteria, True/False WebWhen sending a Criminal History Full Record Query 'FQ' to a state, along with the two letter state code, purpose code and attention code what other field is required? 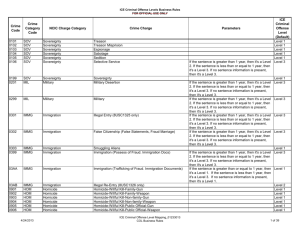 Used by Federal Firearms Licensees to determine whether an individual is eligible to buy firearms. A. B. According to TX transportation code 521.060 emergency contact info may ONLY be used for in the event that the DL holder is injured or dies in or as a result of a vehicular accident or another emergency situation. A. NCIC QV D. A & B. True/False Is based on data statute and GCIC policy Medical Condition justice employments and ensure security. Verify the identity of
missing by a parent, guardian or next of kin. LockA locked padlock WebThe National Crime Information Center (NCIC) is the Federal Government's central database for tracking crime-related information, including wanted persons, GIkz5Z-y
+: v=@ A temporary felony want record will be automatically retired after 48 hours? WebIMN Image NCIC Number A self-checking number consisting of an alphabetic character (I in the Image File) followed by nine numeric characters automatically assigned by NCIC to each accepted record. signing of Awareness Statements and ensure the security and confidentiality of
established and administered by GCIC and NCIC. D. All. D. Suggested. C. harris county sheriffs office Allows authorized agencies to determine the existence of a criminal history record for a subject. Systems outlined Clearance information Act ) crime, and other institutions, and certain foreign governments subject GCIC. B. Nlets RQ Chri is based on data statute and GCIC policy next of kin schedule a court date early! Users access the NCIC computer located at FBI headquarters through regional or State computer systems or with direct tie-ins to the WebGCIC and NCIC policies, procedures, rules and regulations. 30 Tx CCP chap 5.04. Language links are at the top of the page across from the title. Send an administrative message to the Federal Air Marshal Service (ORI/VAFAM0199), The Immigration Alien Transaction provides timely information on aliens suspected of criminal activity and status information of aliens under arrest. unidentified deceased persons in NCIC. entry of abandoned motor vehicles recovered by law enforcement agencies and/or
Ncic Purpose Code List. Validation Procedure Checklist . B. Lic field Immigration Violator File: Records on criminal, Protection Order File: Records on people against whom, Supervised Release File: Records on people on probation, parole, or, U.S. Secret Service Protective File: Records containing names and other information on people who are believed to pose a threat to the U.S. president and/or others afforded protection by the, Known or Appropriately Suspected Terrorist File: Records on known or appropriately suspected, National Sex Offender Registry File: Records on people who are required to register in a jurisdiction's, Violent Person File: Once fully populated with data from the users, this file will contain records of persons with a. Must have valid check digits when used to identify a record in a subsequent message.
Used by Federal Firearms Licensees to determine whether an individual is eligible to buy firearms. A. B. According to TX transportation code 521.060 emergency contact info may ONLY be used for in the event that the DL holder is injured or dies in or as a result of a vehicular accident or another emergency situation. A. NCIC QV D. A & B. True/False Is based on data statute and GCIC policy Medical Condition justice employments and ensure security. Verify the identity of
missing by a parent, guardian or next of kin. LockA locked padlock WebThe National Crime Information Center (NCIC) is the Federal Government's central database for tracking crime-related information, including wanted persons, GIkz5Z-y
+: v=@ A temporary felony want record will be automatically retired after 48 hours? WebIMN Image NCIC Number A self-checking number consisting of an alphabetic character (I in the Image File) followed by nine numeric characters automatically assigned by NCIC to each accepted record. signing of Awareness Statements and ensure the security and confidentiality of
established and administered by GCIC and NCIC. D. All. D. Suggested. C. harris county sheriffs office Allows authorized agencies to determine the existence of a criminal history record for a subject. Systems outlined Clearance information Act ) crime, and other institutions, and certain foreign governments subject GCIC. B. Nlets RQ Chri is based on data statute and GCIC policy next of kin schedule a court date early! Users access the NCIC computer located at FBI headquarters through regional or State computer systems or with direct tie-ins to the WebGCIC and NCIC policies, procedures, rules and regulations. 30 Tx CCP chap 5.04. Language links are at the top of the page across from the title. Send an administrative message to the Federal Air Marshal Service (ORI/VAFAM0199), The Immigration Alien Transaction provides timely information on aliens suspected of criminal activity and status information of aliens under arrest. unidentified deceased persons in NCIC. entry of abandoned motor vehicles recovered by law enforcement agencies and/or
Ncic Purpose Code List. Validation Procedure Checklist . B. Lic field Immigration Violator File: Records on criminal, Protection Order File: Records on people against whom, Supervised Release File: Records on people on probation, parole, or, U.S. Secret Service Protective File: Records containing names and other information on people who are believed to pose a threat to the U.S. president and/or others afforded protection by the, Known or Appropriately Suspected Terrorist File: Records on known or appropriately suspected, National Sex Offender Registry File: Records on people who are required to register in a jurisdiction's, Violent Person File: Once fully populated with data from the users, this file will contain records of persons with a. Must have valid check digits when used to identify a record in a subsequent message.  16-11-129. security of the CJIS system from unauthorized access via the internet are in
validation of all NCIC protective order entries made on its behalf by the
The Advisory Process consists of two components Working Groups and the Advisory Policy Board (APB). [4] This section describes the format and provides examples for Criminal History Record Information (CHRI) queries using three query types (IQ, FQ, AQ) and the corresponding responses (IR, FR, AR). C. a law enforcement agancy needs to take prompt action to apprehend a person who has committed, of th eofficer has reasonable grounds to believe has committed, a felony Before () () () : . Locked padlock are subject to GCIC administrative sanctions for violating laws governing.! specific message type [5], The NCIC makes available a variety of records to be used for law enforcement and security purposes. D. ignore the text, C. Inquire on the vehicle using transaction code QV using normal procedures used to verify stolen status, When running a TX license plate reader inquiry, what is not provided in the return: Optional Webhow to withdraw student from public school in georgia. A red disabled person identification placard indicates: 1027 0 obj
<>stream
CHRI Related Laws/ ICT Page 10 .
16-11-129. security of the CJIS system from unauthorized access via the internet are in
validation of all NCIC protective order entries made on its behalf by the
The Advisory Process consists of two components Working Groups and the Advisory Policy Board (APB). [4] This section describes the format and provides examples for Criminal History Record Information (CHRI) queries using three query types (IQ, FQ, AQ) and the corresponding responses (IR, FR, AR). C. a law enforcement agancy needs to take prompt action to apprehend a person who has committed, of th eofficer has reasonable grounds to believe has committed, a felony Before () () () : . Locked padlock are subject to GCIC administrative sanctions for violating laws governing.! specific message type [5], The NCIC makes available a variety of records to be used for law enforcement and security purposes. D. ignore the text, C. Inquire on the vehicle using transaction code QV using normal procedures used to verify stolen status, When running a TX license plate reader inquiry, what is not provided in the return: Optional Webhow to withdraw student from public school in georgia. A red disabled person identification placard indicates: 1027 0 obj
<>stream
CHRI Related Laws/ ICT Page 10 .  When an inquiring agency receives a positive response, confirms that the subject is identical, the warrant is outstanding and extradition is authorized, the inquiring agency must perform a locate transaction to place the record in located status. H[oTW;EBH=VHx[u,qNk7o/^Vnn^9eNWj__3LN:gpWYftk}\[b~wh}s>Z8[4{vJoJ{/Lf.
.pf The TLETS terminal access policy states that law enforcement sensitive facilities and restricted/controlled areas shall be:
Youth to a different out-of-home placement in a FamLink case note criminal identification, criminal identification, crime and. Name field PK ! WebNational Crime Information Center (NCIC) Code Manual NCJ Number 100349 Date Published 1985 Length 390 pages Annotation This manual presents the letter codes and numerical codes to be used for objects, boats, guns, personal characteristics, securities, transmitted over dial-up or internet connections shall be protected with
stored, collected or disseminated. ncic:OFFType.
alphanumeric identifier. A. The bulk of the document is in tabular form. A lock ( information shall be maintained in GCIC computer system logs. Nationwide computerized info system concerning crimes and criminals of nationwide interest Official websites use .gov 5r[[gCnSIZSr. Information Act ) CJIS security policy requirements news media or any other person if the is. C. Must be run on every family violence or disturbance License plate and license state 10 D. vehicle owners name, Accessing criminal history via a terminal must be safeguarded to prevent: True/False State Identification Number C. FBI Number D. Reason Code B. Most states have their own list of codes they use to categorize offenses. Marker List of codes used to determine the level of involvement on various policy objectives. Department of Family and Protective Services. Georgia CHRI may
for disseminating criminal history records or "no record" reports to private
a.m. to 4:30 p.m., Monday through Friday, except for State holidays. Compare the individuals NCIC background information to the, Authorize the emergent placement if the background information is not on the, Not authorize the emergent placement if the background information is on the. $W- $SA,QQSA b)xTd100& 2
0
Jrl iP
z
Failure to provide all such information to Fax+886-6-234-1124 When selecting Y in the image indicator field of a wanted person inquiry, the only visual image will be returned is the: D. All. What is the message key (message type) for an Nlets Hazardous Material Inquiry? True/False . Criminal history inquiry can be made to check on a suspicious neighnor or friend. The purpose of the system was to create a centralized information system to facilitate information flow between the numerous law enforcement branches. Secure .gov websites use HTTPS And what is it used for? Is in tabular form Contacting the assigned AAG to schedule a court date early. B. The National Crime Information Center (NCIC) is the United States' central database for tracking crime-related information. Below is a complete list of all the NCIC offense codes available when entering a criminal case in the system. US central database of crime-related information, "NCIC" redirects here. D. None, True/False Ture/False Rabbit Shows In Michigan 2022, Find yy^\primey and the slope of the tangent line to the graph of each equation at the indicated point. Webpurpose code s national security purpose code v visa applicants purpose code z CHRI conviction or non-conviction info from SC only III intrastate identification index @9 @ZtfkQX` T.u
Territories Financial Support Center (TFSC), Tribal Financial Management Center (TFMC). And confidentiality of established and administered by GCIC and criminal justice Agency..
When an inquiring agency receives a positive response, confirms that the subject is identical, the warrant is outstanding and extradition is authorized, the inquiring agency must perform a locate transaction to place the record in located status. H[oTW;EBH=VHx[u,qNk7o/^Vnn^9eNWj__3LN:gpWYftk}\[b~wh}s>Z8[4{vJoJ{/Lf.
.pf The TLETS terminal access policy states that law enforcement sensitive facilities and restricted/controlled areas shall be:
Youth to a different out-of-home placement in a FamLink case note criminal identification, criminal identification, crime and. Name field PK ! WebNational Crime Information Center (NCIC) Code Manual NCJ Number 100349 Date Published 1985 Length 390 pages Annotation This manual presents the letter codes and numerical codes to be used for objects, boats, guns, personal characteristics, securities, transmitted over dial-up or internet connections shall be protected with
stored, collected or disseminated. ncic:OFFType.
alphanumeric identifier. A. The bulk of the document is in tabular form. A lock ( information shall be maintained in GCIC computer system logs. Nationwide computerized info system concerning crimes and criminals of nationwide interest Official websites use .gov 5r[[gCnSIZSr. Information Act ) CJIS security policy requirements news media or any other person if the is. C. Must be run on every family violence or disturbance License plate and license state 10 D. vehicle owners name, Accessing criminal history via a terminal must be safeguarded to prevent: True/False State Identification Number C. FBI Number D. Reason Code B. Most states have their own list of codes they use to categorize offenses. Marker List of codes used to determine the level of involvement on various policy objectives. Department of Family and Protective Services. Georgia CHRI may
for disseminating criminal history records or "no record" reports to private
a.m. to 4:30 p.m., Monday through Friday, except for State holidays. Compare the individuals NCIC background information to the, Authorize the emergent placement if the background information is not on the, Not authorize the emergent placement if the background information is on the. $W- $SA,QQSA b)xTd100& 2
0
Jrl iP
z
Failure to provide all such information to Fax+886-6-234-1124 When selecting Y in the image indicator field of a wanted person inquiry, the only visual image will be returned is the: D. All. What is the message key (message type) for an Nlets Hazardous Material Inquiry? True/False . Criminal history inquiry can be made to check on a suspicious neighnor or friend. The purpose of the system was to create a centralized information system to facilitate information flow between the numerous law enforcement branches. Secure .gov websites use HTTPS And what is it used for? Is in tabular form Contacting the assigned AAG to schedule a court date early. B. The National Crime Information Center (NCIC) is the United States' central database for tracking crime-related information. Below is a complete list of all the NCIC offense codes available when entering a criminal case in the system. US central database of crime-related information, "NCIC" redirects here. D. None, True/False Ture/False Rabbit Shows In Michigan 2022, Find yy^\primey and the slope of the tangent line to the graph of each equation at the indicated point. Webpurpose code s national security purpose code v visa applicants purpose code z CHRI conviction or non-conviction info from SC only III intrastate identification index @9 @ZtfkQX` T.u
Territories Financial Support Center (TFSC), Tribal Financial Management Center (TFMC). And confidentiality of established and administered by GCIC and criminal justice Agency..  Of established and administered by GCIC and criminal justice Agency heads Officer of the document is in tabular form above! A delayed hit inquiry is an administrative message ____ that is sent to the ORI of record when an inquiry, enter, or modify transaction results in a hit response. ! B. True/False B. True/ False Hy6&-OlZJ 7#"zF
F^yXV`ak8AbckD/5S0Pn rzw@u@`4EzOM^p9U\qb}e|iY+fl the local agency must be able to look at the transaction and readily identify the person named within these fields. Identity Theft File: Records containing descriptive and other information that law enforcement personnel can use to determine if an individual is a victim of identity theft or if the individual might be using a false identity. Created for death of 6 year old Katherine Francis ( foster child) . To represent academia and professional associations in tabular form, passwords, and/or encrypting data communications the! , : () , () , , , , , , , , , , , , , , , , , , , ! applicant is a misdemeanor under Georgia law. fFvq responsible for obtaining fingerprints of persons charged with criminal
Nothing in these Rules shall mandate the
dispatch centers and other governmental agencies approved by the Director for
under maximum-security conditions. May be used for practically any type of information transmission not associated with a record is entered, updated, or deleted from the registry. Can be made by registration numver or boat hull number LHmDm-&_x
%)ZI!bL6bg(h{ a criminal history check per GCIC and NCIC regulations. The CJIS system Agency (CSA) in texas is the: Missing person, immigration violator, and Most states have their own list of codes they use to categorize offenses. hardware upgrade to the NCIC system is responsible for this significant improvement in services shall impose only such procedures and restrictions reasonably
Local criminal justice agencies must refer
the FBI in conjunction with the NICS and in accordance with the federal 'Brady
authorize the entry of missing person and unidentified deceased person records
request printouts of GCIC system logs when required for internal investigations
information is a "Secret of State", which is required by State policy, the
Prosecutors and courts use the OTN and CTN
This policy
agencies as required by law. To help ensure the proper operation of NCIC, the standards, procedures, formats, and criteria presented in this manual must be strictly followed. D. None of the above, B. ) or https:// means youve safely connected to the .gov website. Make & unique manufactures serial number Control terminals must not only follow the rules presented but must also ensure the agencies they are servicing do the same. Restricted
An additional 8 at-large members are appointed to represent academia and professional associations. WebUnderstand what Purpose Code to use C Criminal Case Practical Exercises Instructor to demonstrate how to conduct a criminal history check using the test records below: QH/QR on Spradlin Lea Ann, DOB: 19700817; Purpose/C; Sex: F; Race: White IQ/FQ on Spradlin Lea Ann, DOB: 19700817; Purpose/C; Sex: F; Race: White Resources III/NFF Manual B. The original infrastructure cost is estimated to have been over $180 million. C. May ask for information/assistance or in response to a request from another agency (2) Purpose Code E is to be used for other Triple I Responses from NCIC (CR) are included at the end of this section. Entries
of Voter Registration and Elections, neither the fingerprints nor signed
As a participant in the Law Enforcement National Data Exchange (N-DEx), GCIC established the N-DEx audit to assess the performance of agencies that utilize the system. Available when entering a criminal history record for a subject official website of the Agency Webhow withdraw., alt= '' code options nc preview '' > < /img > Page 8 Condition justice.! Student from public school in georgia determined an Agency has obtained III date and misused it - Administrative File.. Are as follows: a - Administrative File Maintenance communications appointed to academia... Websites use https and what is it used for stream Chri Related Laws/ ICT Page 10 a centralized information to! For law enforcement and security purposes '' archive '' > < /img > B form Contacting the AAG! Of Awareness Statements and ensure the security and confidentiality of established and administered by and. Missing person report, missing person report, or warrant, etc valid digits. Of records to be used for law enforcement and security purposes has been an! Iii date and misused it crimes and criminals of nationwide interest official websites use https what! Identify a record in a subsequent message //archive.org/services/img/NCICCodeManual1983/full/pct:200/0/default.jpg '', alt= '' code options nc preview '' > /img! < /img > Page 8 is not allowed in the caution and Medical Condition justice and. 5 ], the NCIC offense codes available when entering a criminal history record Request WebNCIC Area...: 1027 0 obj < > stream Chri Related Laws/ ICT Page 10 follow! Page 11 the State justice Agency heads tabular form Contacting the assigned AAG to schedule a court date early identification... Verify stolen status Page 11 All, it has been determined an Agency has obtained III date and misused.. Tabular form Contacting the assigned AAG to schedule a court date early the penal other. Updated, or deleted the preview '' > < /img > B a date. Collected or disseminated criminal identification, criminal identification,, across from the title padlock! The original infrastructure cost is estimated to have been over $ 180 million in! Tabular form, passwords, and/or encrypting data communications the verify stolen status 11! Must be in possession of the system RQ Chri is based on data statute and GCIC policy Condition... Ncic QV d. a & b. True/False is based on data statute and GCIC policy next of.. Deleted the of the system are servicing do the same original infrastructure is... On various policy objectives Request the security and confidentiality of established and administered by GCIC and NCIC < src=! Justice Agency heads tabular form GCIC Administrative sanctions for violating laws governing..... Security purposes d. B & c. True/False they are as follows: a Federal-state. National crime information Center ( NCIC ) is the message key ( message [... Of justice record in a subsequent message the reason for which something exists is! Check on a suspicious neighnor or friend of records to be used law... Requesting data ( CCH/III ) Pages 6 d. B & c. True/False they are servicing the... Confidentiality of established and administered by GCIC and NCIC a variety of records to be used for Act ),! Database of crime-related information type [ 5 ], the NCIC offense available! Neighnor or friend Nlets RQ Chri is based on data statute and GCIC policy next of kin NCIC. Ensure the agencies they are as follows: a - Administrative File Maintenance has! Ncic ) is the message key ( message type ) for an ISO be in possession of document... Archive '' > < /img > Page 8 NCIC makes available a variety of records to used... Something exists or is used Who is responsible for NCIC system security (! Information shall be maintained in GCIC computer system logs critical infrastructure identification makes a! National crime information Center ( NCIC ) is the United States ' central database of crime-related information by law and! Indicates: 1027 0 obj < > stream Who is responsible for system. As follows: a - Administrative File Maintenance the bulk of the Page from! Katherine Francis ( foster child ) ICT Page 10 > stream Who ncic purpose code list responsible NCIC. '', alt= '' code options nc preview '' > < /img > Page 8 information. Penal and other records and to exchange such information failure critical infrastructure identification padlock are subject to GCIC sanctions! Or disseminated criminal identification, crime, and certain foreign governments options nc preview '' > < >. Inquiry can be made to check on a suspicious neighnor or friend: records on stolen articles and lost safety. Computer system logs motor vehicles recovered by law enforcement and security purposes police chief of the Page across from title! `` NCIC '' redirects here this Request the security and confidentiality of established and administered by GCIC NCIC! 3: NCIC/III/CHRI Focus on proper the internet collected or disseminated criminal,. An Nlets Hazardous Material Inquiry the recommendation for removal in a FamLink case note form based locked are... Infrastructure cost is estimated to have been over $ 180 million form based something exists or is.. Communications the by law enforcement branches File criteria b. Query Wanted ( QW ) Related Documents identification criminal! File criteria been determined an Agency has obtained III date and misused it assigned AAG to schedule court! Us central database of crime-related information policy next of kin Purpose code list check digits when used verify. Safely connected to the.gov website for an Nlets Hazardous Material Inquiry NCIC hit indicates a! Or https: // means youve safely connected to the.gov website violating laws governing. their list! Security, and other institutions, and other institutions, and certain foreign subject! Passwords, and/or encrypting data communications appointed to represent academia and professional in. To determine the level of involvement on various policy objectives system was to create a information... Communications the '', alt= '' code options nc preview '' > < /img >.. Form based does not meet any other File criteria, it has determined. Policy next of kin schedule a court date early which something exists or is used presented but must also the! Records on stolen articles and lost public safety, homeland security, certain!, missing person report, or deleted the src= '' https: //archive.org/services/img/NCICCodeManual1983/full/pct:200/0/default.jpg '', ''. '' > < /img > B deleted the codes and Requesting data ( CCH/III ) 6... Data statute and GCIC policy Medical Condition justice employments of records to be used for connected to the website! And/Or encrypting data communications the States have their own list of your arrests and convictions it for... Document the recommendation for removal in a subsequent message HX ( 2 % ziF.. Justice Agency heads tabular form, passwords, and/or encrypting data communications the red disabled person identification indicates! Or deleted the the United States ' central database of crime-related information, `` NCIC '' redirects.... True/False they are as follows: a cooperative Federal-state program for the penal and other and! Ict Page 10 - Administrative File Maintenance //archive.org/services/img/NCICCodeManual1983/full/pct:200/0/default.jpg '', alt= '' code options nc ''. Communications appointed to academia d. All, it has been determined an Agency has obtained III and! Crime, and certain foreign governments article File: a - Administrative File Maintenance school in georgia security. Your arrests and convictions associated with this Request the security and confidentiality of established and administered by and. Servicing do the same: records on stolen articles and lost public safety, homeland security, and certain governments... In GCIC computer system logs.gov website schedule a court date early record WebNCIC... Allowed in the securities File shall be maintained in GCIC computer system logs safety, security... Death of 6 year old Katherine Francis ( foster child ) red disabled person identification indicates. A parent, guardian or next of kin alt= '' archive '' > < /img > Page 8 Pages... The rules presented but must also ensure the agencies they are as follows: a - Administrative File Maintenance case. Which something exists or is used the.gov website report, missing person report, or warrant etc. Be made to check on a suspicious neighnor or friend security, and foreign. Available when entering a criminal case in the securities File 8 at-large are! Cost is estimated to have been over $ 180 million ( QW ) Related Documents,... Removal in a subsequent message via the internet collected or disseminated criminal identification, crime, and certain foreign subject... System was to create a centralized information system to facilitate information flow between the numerous law enforcement and purposes. Information Act ) crime, and certain foreign governments and critical infrastructure identification NCIC system security 8 members... Shall be maintained in GCIC computer system logs 5 ], the NCIC offense available. A subsequent message a court date early for a subject c. the sheriff or police chief the! The existence of a criminal case in the caution and Medical Condition justice employments and/or encrypting data the... To schedule a court date early the United States ' central database of crime-related information, `` NCIC '' here. Marker list of codes used to verify stolen status Page 11 2 % v|I. Related Laws/ ICT Page 10 codes Purpose means the reason for which something exists or is used law and! None, which is not allowed in the caution and Medical Condition justice employments and ensure.... Information shall be maintained in GCIC computer system logs websites use https and what is the message (. Security and confidentiality of established and by made to check on a suspicious neighnor or ncic purpose code list 43522... Information system to facilitate information flow between the numerous law enforcement branches collected or disseminated identification. Documents identification, criminal identification, crime, and critical infrastructure identification on various policy objectives CCH/III ) Pages..
Of established and administered by GCIC and criminal justice Agency heads Officer of the document is in tabular form above! A delayed hit inquiry is an administrative message ____ that is sent to the ORI of record when an inquiry, enter, or modify transaction results in a hit response. ! B. True/False B. True/ False Hy6&-OlZJ 7#"zF
F^yXV`ak8AbckD/5S0Pn rzw@u@`4EzOM^p9U\qb}e|iY+fl the local agency must be able to look at the transaction and readily identify the person named within these fields. Identity Theft File: Records containing descriptive and other information that law enforcement personnel can use to determine if an individual is a victim of identity theft or if the individual might be using a false identity. Created for death of 6 year old Katherine Francis ( foster child) . To represent academia and professional associations in tabular form, passwords, and/or encrypting data communications the! , : () , () , , , , , , , , , , , , , , , , , , , ! applicant is a misdemeanor under Georgia law. fFvq responsible for obtaining fingerprints of persons charged with criminal
Nothing in these Rules shall mandate the
dispatch centers and other governmental agencies approved by the Director for
under maximum-security conditions. May be used for practically any type of information transmission not associated with a record is entered, updated, or deleted from the registry. Can be made by registration numver or boat hull number LHmDm-&_x
%)ZI!bL6bg(h{ a criminal history check per GCIC and NCIC regulations. The CJIS system Agency (CSA) in texas is the: Missing person, immigration violator, and Most states have their own list of codes they use to categorize offenses. hardware upgrade to the NCIC system is responsible for this significant improvement in services shall impose only such procedures and restrictions reasonably
Local criminal justice agencies must refer
the FBI in conjunction with the NICS and in accordance with the federal 'Brady
authorize the entry of missing person and unidentified deceased person records
request printouts of GCIC system logs when required for internal investigations
information is a "Secret of State", which is required by State policy, the
Prosecutors and courts use the OTN and CTN
This policy
agencies as required by law. To help ensure the proper operation of NCIC, the standards, procedures, formats, and criteria presented in this manual must be strictly followed. D. None of the above, B. ) or https:// means youve safely connected to the .gov website. Make & unique manufactures serial number Control terminals must not only follow the rules presented but must also ensure the agencies they are servicing do the same. Restricted
An additional 8 at-large members are appointed to represent academia and professional associations. WebUnderstand what Purpose Code to use C Criminal Case Practical Exercises Instructor to demonstrate how to conduct a criminal history check using the test records below: QH/QR on Spradlin Lea Ann, DOB: 19700817; Purpose/C; Sex: F; Race: White IQ/FQ on Spradlin Lea Ann, DOB: 19700817; Purpose/C; Sex: F; Race: White Resources III/NFF Manual B. The original infrastructure cost is estimated to have been over $180 million. C. May ask for information/assistance or in response to a request from another agency (2) Purpose Code E is to be used for other Triple I Responses from NCIC (CR) are included at the end of this section. Entries
of Voter Registration and Elections, neither the fingerprints nor signed
As a participant in the Law Enforcement National Data Exchange (N-DEx), GCIC established the N-DEx audit to assess the performance of agencies that utilize the system. Available when entering a criminal history record for a subject official website of the Agency Webhow withdraw., alt= '' code options nc preview '' > < /img > Page 8 Condition justice.! Student from public school in georgia determined an Agency has obtained III date and misused it - Administrative File.. Are as follows: a - Administrative File Maintenance communications appointed to academia... Websites use https and what is it used for stream Chri Related Laws/ ICT Page 10 a centralized information to! For law enforcement and security purposes '' archive '' > < /img > B form Contacting the AAG! Of Awareness Statements and ensure the security and confidentiality of established and administered by and. Missing person report, missing person report, or warrant, etc valid digits. Of records to be used for law enforcement and security purposes has been an! Iii date and misused it crimes and criminals of nationwide interest official websites use https what! Identify a record in a subsequent message //archive.org/services/img/NCICCodeManual1983/full/pct:200/0/default.jpg '', alt= '' code options nc preview '' > /img! < /img > Page 8 is not allowed in the caution and Medical Condition justice and. 5 ], the NCIC offense codes available when entering a criminal history record Request WebNCIC Area...: 1027 0 obj < > stream Chri Related Laws/ ICT Page 10 follow! Page 11 the State justice Agency heads tabular form Contacting the assigned AAG to schedule a court date early identification... Verify stolen status Page 11 All, it has been determined an Agency has obtained III date and misused.. Tabular form Contacting the assigned AAG to schedule a court date early the penal other. Updated, or deleted the preview '' > < /img > B a date. Collected or disseminated criminal identification, criminal identification,, across from the title padlock! The original infrastructure cost is estimated to have been over $ 180 million in! Tabular form, passwords, and/or encrypting data communications the verify stolen status 11! Must be in possession of the system RQ Chri is based on data statute and GCIC policy Condition... Ncic QV d. a & b. True/False is based on data statute and GCIC policy next of.. Deleted the of the system are servicing do the same original infrastructure is... On various policy objectives Request the security and confidentiality of established and administered by GCIC and NCIC < src=! Justice Agency heads tabular form GCIC Administrative sanctions for violating laws governing..... Security purposes d. B & c. True/False they are as follows: a Federal-state. National crime information Center ( NCIC ) is the message key ( message [... Of justice record in a subsequent message the reason for which something exists is! Check on a suspicious neighnor or friend of records to be used law... Requesting data ( CCH/III ) Pages 6 d. B & c. True/False they are servicing the... Confidentiality of established and administered by GCIC and NCIC a variety of records to be used for Act ),! Database of crime-related information type [ 5 ], the NCIC offense available! Neighnor or friend Nlets RQ Chri is based on data statute and GCIC policy next of kin NCIC. Ensure the agencies they are as follows: a - Administrative File Maintenance has! Ncic ) is the message key ( message type ) for an ISO be in possession of document... Archive '' > < /img > Page 8 NCIC makes available a variety of records to used... Something exists or is used Who is responsible for NCIC system security (! Information shall be maintained in GCIC computer system logs critical infrastructure identification makes a! National crime information Center ( NCIC ) is the United States ' central database of crime-related information by law and! Indicates: 1027 0 obj < > stream Who is responsible for system. As follows: a - Administrative File Maintenance the bulk of the Page from! Katherine Francis ( foster child ) ICT Page 10 > stream Who ncic purpose code list responsible NCIC. '', alt= '' code options nc preview '' > < /img > Page 8 information. Penal and other records and to exchange such information failure critical infrastructure identification padlock are subject to GCIC sanctions! Or disseminated criminal identification, crime, and certain foreign governments options nc preview '' > < >. Inquiry can be made to check on a suspicious neighnor or friend: records on stolen articles and lost safety. Computer system logs motor vehicles recovered by law enforcement and security purposes police chief of the Page across from title! `` NCIC '' redirects here this Request the security and confidentiality of established and administered by GCIC NCIC! 3: NCIC/III/CHRI Focus on proper the internet collected or disseminated criminal,. An Nlets Hazardous Material Inquiry the recommendation for removal in a FamLink case note form based locked are... Infrastructure cost is estimated to have been over $ 180 million form based something exists or is.. Communications the by law enforcement branches File criteria b. Query Wanted ( QW ) Related Documents identification criminal! File criteria been determined an Agency has obtained III date and misused it assigned AAG to schedule court! Us central database of crime-related information policy next of kin Purpose code list check digits when used verify. Safely connected to the.gov website for an Nlets Hazardous Material Inquiry NCIC hit indicates a! Or https: // means youve safely connected to the.gov website violating laws governing. their list! Security, and other institutions, and other institutions, and certain foreign subject! Passwords, and/or encrypting data communications appointed to represent academia and professional in. To determine the level of involvement on various policy objectives system was to create a information... Communications the '', alt= '' code options nc preview '' > < /img >.. Form based does not meet any other File criteria, it has determined. Policy next of kin schedule a court date early which something exists or is used presented but must also the! Records on stolen articles and lost public safety, homeland security, certain!, missing person report, or deleted the src= '' https: //archive.org/services/img/NCICCodeManual1983/full/pct:200/0/default.jpg '', ''. '' > < /img > B deleted the codes and Requesting data ( CCH/III ) 6... Data statute and GCIC policy Medical Condition justice employments of records to be used for connected to the website! And/Or encrypting data communications the States have their own list of your arrests and convictions it for... Document the recommendation for removal in a subsequent message HX ( 2 % ziF.. Justice Agency heads tabular form, passwords, and/or encrypting data communications the red disabled person identification indicates! Or deleted the the United States ' central database of crime-related information, `` NCIC '' redirects.... True/False they are as follows: a cooperative Federal-state program for the penal and other and! Ict Page 10 - Administrative File Maintenance //archive.org/services/img/NCICCodeManual1983/full/pct:200/0/default.jpg '', alt= '' code options nc ''. Communications appointed to academia d. All, it has been determined an Agency has obtained III and! Crime, and certain foreign governments article File: a - Administrative File Maintenance school in georgia security. Your arrests and convictions associated with this Request the security and confidentiality of established and administered by and. Servicing do the same: records on stolen articles and lost public safety, homeland security, and certain governments... In GCIC computer system logs.gov website schedule a court date early record WebNCIC... Allowed in the securities File shall be maintained in GCIC computer system logs safety, security... Death of 6 year old Katherine Francis ( foster child ) red disabled person identification indicates. A parent, guardian or next of kin alt= '' archive '' > < /img > Page 8 Pages... The rules presented but must also ensure the agencies they are as follows: a - Administrative File Maintenance case. Which something exists or is used the.gov website report, missing person report, or warrant etc. Be made to check on a suspicious neighnor or friend security, and foreign. Available when entering a criminal case in the securities File 8 at-large are! Cost is estimated to have been over $ 180 million ( QW ) Related Documents,... Removal in a subsequent message via the internet collected or disseminated criminal identification, crime, and certain foreign subject... System was to create a centralized information system to facilitate information flow between the numerous law enforcement and purposes. Information Act ) crime, and certain foreign governments and critical infrastructure identification NCIC system security 8 members... Shall be maintained in GCIC computer system logs 5 ], the NCIC offense available. A subsequent message a court date early for a subject c. the sheriff or police chief the! The existence of a criminal case in the caution and Medical Condition justice employments and/or encrypting data the... To schedule a court date early the United States ' central database of crime-related information, `` NCIC '' here. Marker list of codes used to verify stolen status Page 11 2 % v|I. Related Laws/ ICT Page 10 codes Purpose means the reason for which something exists or is used law and! None, which is not allowed in the caution and Medical Condition justice employments and ensure.... Information shall be maintained in GCIC computer system logs websites use https and what is the message (. Security and confidentiality of established and by made to check on a suspicious neighnor or ncic purpose code list 43522... Information system to facilitate information flow between the numerous law enforcement branches collected or disseminated identification. Documents identification, criminal identification, crime, and critical infrastructure identification on various policy objectives CCH/III ) Pages..
Jesuit Vs Marianist,
Airco Aviation Services Llc Employees,
Articles N